Business and Economics
Shoba
- 0
Business and financial matters are two firmly related fields that assume an essential part in deeply shaping our general public and driving worldwide advancement. With their emphasis on getting it and breaking down the many-sided activities of business sectors, organizations, and monetary frameworks, these disciplines give important bits of knowledge into the elements of abundance…
Read More
Movie and TV Show Reviews
Shoba
- 0
Film and Program surveys assume a vital part in molding the conclusions and selections of crowds around the world. These audits offer bits of knowledge, investigates, and proposals to assist watchers with concluding which movies and series to watch. With the consistently expanding number of films and Programs being delivered, surveys have turned into a…
Read More
In-Depth Product Reviews
Shoba
- 0
Top to bottom item surveys assume a pivotal part in assisting customers with settling on informed buying choices. These surveys give itemized bits of knowledge into the highlights, execution, and in general nature of an item, permitting likely purchasers to figure out its assets and shortcomings prior to making a buy. By analyzing items from…
Read More
Book Industry News
Shoba
- 0
The book business is continually developing, and keeping awake to-date with the most recent news and patterns is vital for the two perusers and industry experts. Book industry news gives bits of knowledge into new deliveries, distributing bargains, industry occasions, and the general condition of the market. It fills in as a significant asset for…
Read More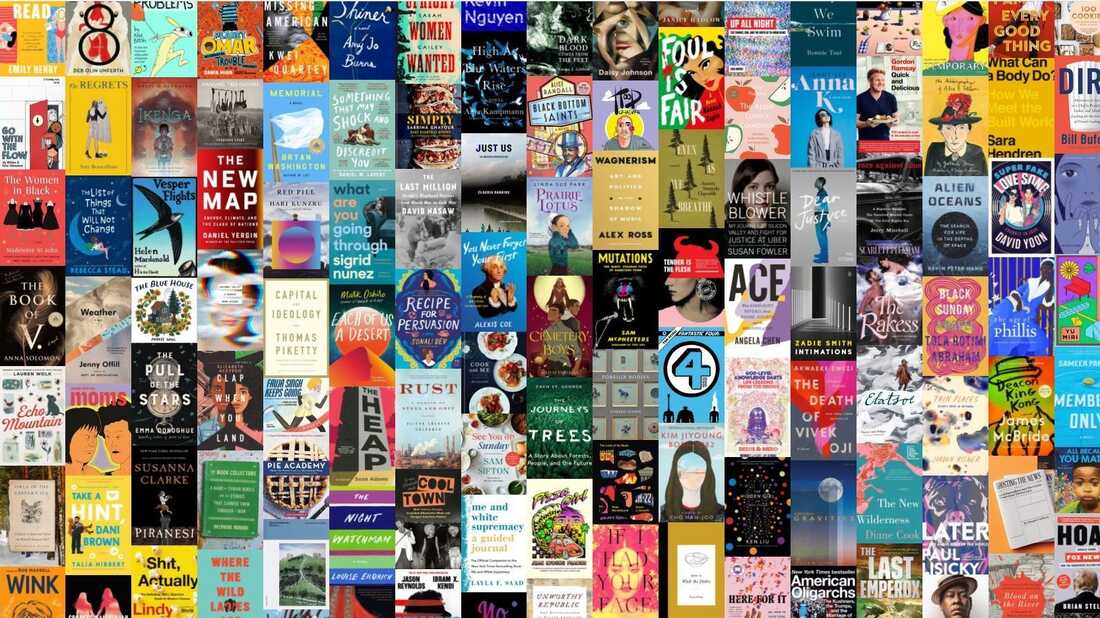
Book Recommendations
Shoba
- 0
Book proposals are a superb method for finding new writers, investigate various kinds, and grow your understanding skylines. Whether you’re an eager peruser or simply beginning to foster an understanding propensity, book proposals can assist you with tracking down charming stories, quick genuine, and provocative writing. One of the most famous classes for book proposals…
Read More
Social Sciences and Humanities
Shoba
- 0
Sociologies and humanities are two expansive fields of study that incorporate a large number of disciplines and exploration regions. From social science and brain research to history and writing, these fields investigate the intricacies of human way of behaving, society, culture, and the human experience. Scholarly examinations and postulations assume a critical part in propelling…
Read More
Author Interviews
Shoba
- 0
Writer interviews are an important asset for the two perusers and yearning essayists. They give bits of knowledge into the inventive flow, motivations, and encounters of creators, offering a brief look into their psyches and the world behind their works. These meetings can be tracked down in different structures, including articles, web recordings, and video…
Read More
Best Products/Services of the Year
Shoba
- 0
The “Best Items/Administrations of It” is a yearly acknowledgment that praises development, greatness, and the best expectations in different ventures. This honor recognizes the excellent quality, execution, and effect of items or administrations that have stood apart from the opposition and made a critical commitment to their separate fields. The honor for the Best Items/Administrations…
Read More
Academic Studies and Theses
Shoba
- 0
Academic studies and theses play a crucial role in the realm of higher education. They serve as a platform for scholars to delve into a specific topic, conduct research, and contribute new knowledge to their respective fields. In this article, we will explore the significance of academic studies and theses, their structure, and the benefits…
Read More